Risk Register analysis
(→Elements of Risk Register) |
(→Elements of Risk Register) |
||
| Line 12: | Line 12: | ||
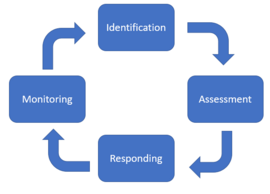
As can be seen in figure 1, the implementation of the risk register model follows four processes. Firstly, the risks have to be identified. Secondly, they have to be assessed based on their impact and probability. After risk assessment, it is important to define the actions that must be taken, in order to manage the risks. The final process of the risk register model follows, deals with the ways the risks can be monitored. <ref name="Pmi" />, <ref name="ot" /> The outcome of the previously mentioned processes is the input for the risk register framework. | As can be seen in figure 1, the implementation of the risk register model follows four processes. Firstly, the risks have to be identified. Secondly, they have to be assessed based on their impact and probability. After risk assessment, it is important to define the actions that must be taken, in order to manage the risks. The final process of the risk register model follows, deals with the ways the risks can be monitored. <ref name="Pmi" />, <ref name="ot" /> The outcome of the previously mentioned processes is the input for the risk register framework. | ||
| − | + | [[File:Screenshot 2021-02-25 221935.png|right|thumb|270px|Figure 1: Implementation steps of Risk Register (own figure, based on <ref name="Pmi" /> and <ref name="PRINCE"/>) ]] | |
Revision as of 09:14, 26 February 2021
Developed by Dorothea Georgiadou
In an age where the economic, social, and political environment is constantly shifting, there is an urgent need to study the risks that may threaten the success of a project. It is particularly important to study the risks that may adversely affect the project and lead to events that might have as a cause the exceeding of the agreed budget and time. For this reason, the risk management planning should identify and describe in detail the potential risks by providing the needed information for the actions that should be done for eliminating their negative impact. The high uncertainty that exists in projects necessitates the use of a management tool that will control the risks. [1] In this article the risk management framework ‘’Risk register’’ is explained. Risk register is a tool that covers and studies many aspects of risk management processes. More specifically, the aim of this article is to explain how this tool can be used for the identification, assessment, and treatment of potential risks. Moreover, the importance of the risk register in the risk analysis process is outlined, as not only the qualitative aspects of a project are taken into consideration but also it prioritizes the risks based on their impact and probability to happen during the implementation phase of a project. This constitutes one of the positive features of this framework as through the analysis of this article it can be concluded that risk register helps project managers to have a better understanding and ways of managing the potential risks. Finally, the article analyzes along with the benefits the limitations of this risk management tool.
Contents |
Why use risk register?
In an ever-changing environment, a projects’ success is associated with a high level of uncertainty. Projects are threatened by external and internal factors throughout their lifecycle and hence the presence of project risk management is more than necessary. In the ‘Practice Standard for Project Risk Management’, risk management is an approach that plays a vital role in the strategic and decision-making processes since adjustments in the project management planning can be done after the identification of the projects’ challenges. The risk register framework is used to support the risk management process in order to eliminate the negative impact that the various threats might have on a project. Threats could come from the external and internal environment of the company. The external risks are associated with the economic, social, political, and technological environment, while the internal threats include risks that are related to human actions and estimations. For example, it is possible for people to make wrong estimations because of inexperience and underestimation of some threats. This high level of uncertainty makes it increasingly necessary to use a model that assists the risk management process in a more effective way. [1]
The role of Risk Register
In ‘Practice Standard for Project Risk Management’, the risk register is defined as the framework that is used in project risk management for the documentation of the identified risks. [1] It records all the needed information that will be the steppingstone to overcome the risks that might menace projects' success. [1] It is worth noting that based on ‘PRINCE2’, the risks are divided into threats and opportunities. Threats are the risks that could have negative consequences for the project, while opportunities could bring positive outcomes to the company. [2] The article is mainly focused on the documentation of the various threats in the risk register. The importance of the tool is hidden in the fact that it can assist project managers with tackling potential threats and to have a better and clearer overview of the internal and external risks that might negatively affect the success of the project. [3] The aim of the risk register is to record information related to the identification, assessment, evaluation of importance, and managing of the potential risks. [1], [2] More specifically, the uncertainty that exists in projects makes it necessary to use a model that provides various information for the events that could threaten the projects. [1]
In the ‘PMBOK guide ’ it is outlined that the tool risk register can be used in different phases of a project. Firstly, it can be used at a very early stage of a project in order to provide information for the risks that might be a threat. Secondly, as the project continues, new threats are recorded and documented in the risk register. In other words, it is used to update the new risks and inform the stakeholders how they should monitor the new threats. Finally, it documents all the risks that have been recorded after the completion of a project. [4]
Elements of Risk Register
As can be seen in figure 1, the implementation of the risk register model follows four processes. Firstly, the risks have to be identified. Secondly, they have to be assessed based on their impact and probability. After risk assessment, it is important to define the actions that must be taken, in order to manage the risks. The final process of the risk register model follows, deals with the ways the risks can be monitored. [1], [4] The outcome of the previously mentioned processes is the input for the risk register framework.
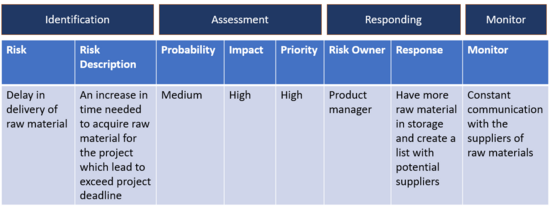
This framework has the form of a table where each column represents different characteristics of the potential risks.[5] One of the risk components analysed in this study is a brief description of every risk the project managers have recognized. [1] This helps the project managers not only to clarify the risks but also to understand why they are threatening the project’s success. Secondly, for the assessment of the risks, their probability and impact on the project are examined. Furthermore, in ‘Practice Standard for Project Risk Management’ it is stated that the evaluation of the risk is depending on their impact and their frequency to happen. For instance, the risks that have high impact and probability to occur, are risks with higher importance than the risks with low frequency and impact. The identification of the risks’ importance is an essential element for project managers to know which risks are needed more attention and time for setting up a plan in order to overcome them. [1] Furthermore, based on the ‘PMBOK guide’ the risk register also includes information about the person who must tackle every risk and the actions that he has to take to eliminate its negative consequences. [4] The above elements are demanding high attention as they are mainly focused on dominant areas of the risk management process which are the identification of the threats, the evaluation of their importance, and the course of action that should be taken.
How Risk register is used
In order to have an in-depth understanding of the risk register, it is of utmost importance to analyse the way that it can be used. The tool aims to eliminate the negative impacts of the various threats by identifying, assessing, evaluating, and monitoring them. The following sections provide a guidance on how the four processes of risk register can be implemented.
1. How to identify the risks.
As a first step, the risks have to be identified by using the right techniques. Once this is complete, a short description of the risks that have been identified through the risk management process is provided.
1.1 Risk identification
As it is quoted in ‘Practice Standard for Project Risk Management’, ‘’ A risk cannot be managed unless it is first identified.’’ [1] The identified risks are the first information that will be used in the risk register. [1], [4] It is worth noting that the risk identification process is continuous because as time passes, the number of information increases. In other words, new risks will become knowable by repeating the risk identification process in different phases of a project. [1]
In this article, three methods are used for the risk identification process and all of them are following the ‘Practice Standard for Project Risk Management’ [1]:
- Historical review: This technique is used as an analysis of events that happened in the past. When this method, is used it is vital to make sure that the events that are under observation are correlated with risks that happened before in this project or in different projects from the same or different company. This method demands attention as there is the risk to compare data and risks from projects that are not closely connected to the project.
- Current Assessment: In this method, the risk identification process is focused on analysing the project’s uncertainty based on the information that is known in this specific period of time.
- Creativity Techniques: This approach is based on the creativity of the people who participate in the project. To be more specific, stakeholders have the chance to work individually or with other people in order to identify risks by using creative methods and thinking outside of the box.
All of the techniques mentioned above have both strong points and limitations. This means that if they are used separately, they might lead to inadequate results. Thus, the combination of the three techniques can guarantee more accurate results. [1]
1.2 Risk description
The description of the identified risks is a very important component of the risk identification process. It is a way to make sure that the risks are well communicated and understood among all the stakeholders. [6] For instance, in a construction problem, it is identified that a potential risk could be a shock in the economy. A potential explanation is that a shock in the economy could increase the price of raw materials and as a result the project might exceed the agreed budget. As it could be observed, the description of this risk could give a better insight into what this change might impact.
2. How to assess the risks
The assessment of the various risks could be applied by using two methods, namely, the qualitative and quantitative risk analysis. Both methods are used to evaluate risks’ importance to the project. This includes an analysis of the probability that each risk has to occur and the impact that they might have on the project. [1] In this article, the assessment of the identified risks is following the ‘’ Practice Standard for Project Risk Management‘’ and the‘’ PMBOK guide ‘’ .
- Qualitative risk analysis
In qualitative risk analysis, the risks are evaluated and ranked based on their probability, impact, and some other characteristics that have been defined before the implementation of the analysis. This analysis is implemented regularly as new threats might need to be identified. The basic components of qualitative risk analysis are the high or low probability of a risk to happen and the consequences that it might have in ‘’ one or more project objectives such as schedule, cost, quality, or performance.’’ [1],[4] Additionally, in qualitative risk analysis the risks can be grouped based on various criteria. For example, they can be grouped by risks that might exceed projects’ deadlines. This way, the project management team could monitor the risks in a more effective way since not only they will know the project areas they need to pay more attention to, but they will also have a quicker response managing the threats of the several categories. [1],[4]
- Quantitative risk analysis
The quantitative risk analysis is used to calculate risks’ effects on the project. While this numerical analysis is not considered vital for all the projects, it provides more pragmatistic results. The implementation of the quantitative risk analysis follows on from the qualitative risk analysis. This could be explained by the fact that in the qualitative risk analysis the risks are already prioritized and thus the most vital threats are recognized and could be calculated. The impact and the probability are calculated, and the risk register table can be updated with numerical results. [1],[4]
3. How to respond to the risks
It is of utmost importance to tackle the identified risks once they have been assessed. In order to do so, it is necessary to perform a risk management plan which will include the actions for dealing with the risks and the person who is responsible to tackle them. As a first step the risks should be communicated and understood by all the stakeholders. Every potential risk is assigned to the right people. These people are called risk owners and they are responsible with controlling and finding solutions for the risks they are assigned with.The risks could harm the project in various ways and for this reason, there should be a plan with responses for all of them. In the ‘Practice Standard for Project Risk Management’ it is written that ’’ the planning entails agreeing upon the actions to be taken and the potential changes to budget, schedule, resources, and scope which these actions might cause.’’ [1] Furthermore, the actions that have to be taken for every risk should be developed at the very early stage of its identification. In other words, it is of utmost importance to have the strategies and responses in advance so that project’s time schedule will change as little as possible. [1] The risk register includes all the responses and actions on its table. Once new risks are identified risk register is updated with new strategies that the risk owner has to follow. Moreover, throughout the lifecycle of a project, it is possible to make adjustments and corrections to the plans of the previously identified risks. [6]
4. How to monitor the risks.
Risk monitoring is the last process of risk register. This final step is as important as the three steps mentioned above. As it is previously mentioned, the project can be threatened not only by new risks but changes to the ones already identified. In the risk register model, all these changes are updated and documented by providing new information for the actions that have changed. [1], [6]
Reflections
Advantages
- Risks are well communicated among stakeholders [1]
Disadvantages
- Time-consuming process
- Need support from other tools
References
- ↑ 1.00 1.01 1.02 1.03 1.04 1.05 1.06 1.07 1.08 1.09 1.10 1.11 1.12 1.13 1.14 1.15 1.16 1.17 1.18 1.19 1.20 1.21 1.22 1.23 PMI Standard for Risk Management (2019)
- ↑ 2.0 2.1 2.2 2.3 Project Management: "Managing Successful Projects with PRINCE2" 6th Edition (2017)
- ↑ https://www.wrike.com/blog/what-is-a-risk-register-project-management/
- ↑ 4.0 4.1 4.2 4.3 4.4 4.5 4.6 Project Management: A guide to the Project Management Body of Knowledge (PMBOK guide) 6th Edition (2017)
- ↑ Project Risk Register Analysis Based on the Theoretical Analysis of Project Management Notion of Risk, Juris Uzulāns, University of Latvia, 2016
- ↑ 6.0 6.1 6.2 https://https://www.projectmanager.com/blog/guide-using-risk-register