Risk Treatment in project management
Contents |
Abstract
In a project, a program, or a portfolio there will always be a number of activities. All these activities will involve risk to some degree – either as a threat or an opportunity. If risks are not managed in the project, program, or portfolio it will be difficult to accomplish success. Therefore, it is important for the project, program, or portfolio leader to manage these risks by identifying them, evaluate them and treat them. The latter will be the focus of this article. Risk Treatment, also referred to as Risk Control, is the discipline within Risk Management that takes place once a risk has been identified and assessed. Here, appropriate measures are put in place to mitigate and reduce all unacceptable risks and to steer them towards an acceptable target level. The identification of the treatment measures should be done from a cost benefit point of view, analysing the cost of treating the risk up against the potential benefits. Furthermore, as time and resource are often a limited factor, the identification and treatment should be focused on the most important risks identified from the preliminary evaluation phase. Risk Treatment is mainly split into four main categories, namely risk avoidance, risk sharing, risk reduction and risk retention. Risk avoidance is the option where one simply avoids the underlying activity that causes the potential risk. Risk sharing is done by transferring either fully or parts of the risk to other stakeholders e.g., by insurance or by outsourcing the related activities externally. Risk reduction is done by removing sources of threats, reducing or removing the severity of vulnerabilities and by generally reducing the likelihood of threats. Lastly, risk retention is the category where the risk is accepted, due to either an acceptable threat level or a too costly treatment given the alternative options. [1] Once appropriate treatment measures have been selected, an action plan should be developed to 1) ensure that the chosen treatment options are communicated and 2) to ensure the chosen measures are implemented and acted on.[2]
Big Idea
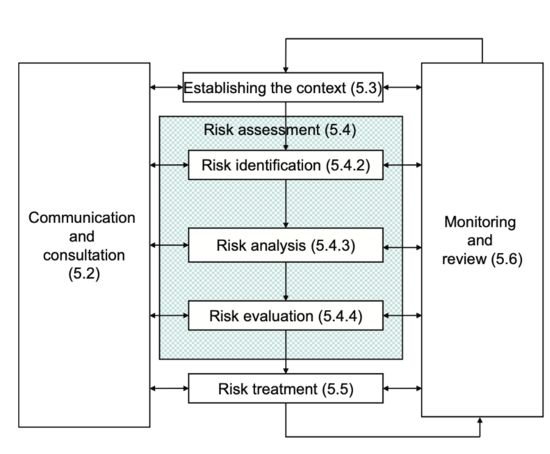
To understand risk treatment, it is first necessary to understand what Risk Management is and where in the Risk Management process the treatment occurs. In the ISO 31000 standard, Risk Management is defined as: “Coordinated activities to direct and control an organization with regard to risk” [3] This means that Risk Management controls several different activities that in combination with each other seeks to protect an organization towards risks. The purpose of risk management is to increase the probability of achieving the main goals and objectives of the project, program, or portfolio. This is done through the Risk Management Process as seen illustrated on figure 1.
First, the context of the project, program or portfolio needs to be established. This is done by articulating objectives, defining the parameters that needs to be considered, both internally and externally, and setting the overall scope of the project, program or portfolio. Secondly, the Risk Assessment phase should be initiated. This phase consists of three steps.
First step is the Risk Identification phase. Here, a comprehensive list of risks related to the project, program or portfolio is made which creates the foundation for the risk analysis. In the risk analysis, all risks from the identification phase are understood by considering their causes and sources, their potential consequences, and the likelihood of occurrence.
The risks are then evaluated based on the analysis. This creates a benchmark for the decision making where risks are to be prioritized, leading the risk management process into the final phase, Risk Treatment. This topic will be expanded further in the following section.
Risk Treatment
As previously described, Risk Treatment is the last activity in the Risk Management process. This is the part of the process where the risk is actually being treated and one tries to mitigate the potential consequences. Risk Treatment both addresses the positive and negatives risks, accordingly also referred to as opportunities and threats. Opportunities are the risks that have the potential to create a positive impact on the project, program or portfolio while threats are the kind of risk that are likely to have a negative impact on the project, program or portfolio. The latter is often the type of risk that people think of when hearing the word risk. [4]
When choosing treatment options, there is mainly four different strategies that can be used [6]:
- Risk Acceptance
- Risk Avoidance
- Risk Mitigation
- Risk Transfer
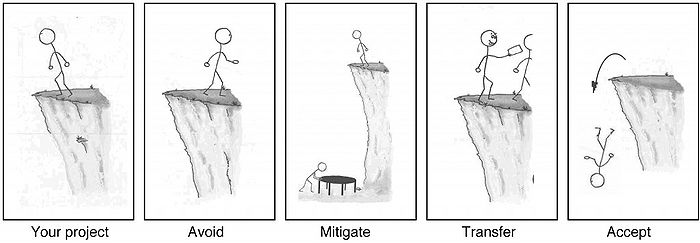
Selecting the strategies can be done by either combining the different options or by solely using one of them. Choosing the most appropriate strategies involves comparing the potential beneficial outcome, derived in relation to the accomplishment of the defined objectives against the monetary cost, the disadvantages of implementation and the effort put into it [1]. The four main strategies are seen expanded below, together with three supplementary strategies; use of contingency, exploitation, and enhancement. Also, a visualization of the four options can be seen on figure 2.
Risk Acceptance
Implementing a treatment always carries a cost to some degree. The cost will often be a direct monetary cost, but can also be an indirect cost shown in for example reduced flexibility in the project, program or portfolio. Therefore, it is necessary to weigh the cost of implementing a treatment up against the benefits of doing so. When choosing to accept a risk, no specific actions are taken to mitigate or provoke the risk, depending on whether it is an opportunity or a threat. The acceptance can be chosen as a strategy because the potential treatment is either too expensive, or because the negative or positive consequences from the risk are without any significant impact [4].
Risk Avoidance
When talking about threats, risk avoidance can be done in to ways. Either, the risk is fully eliminated and thereby avoided and removed from the project, program or portfolio. This means that the project, program or portfolio does not need to change its parameters and scope to steer away from the risk, but rather uses resources on eliminating the risk. [7] This can also be classified as a mitigating action. Or else, the risk is avoided and is thereby still existing, but not relevant to the project, program or portfolio anymore. This is done by changing the parameters, and asking yourself the question: "How can this project, program or portfolio be redesigned so that the risk in question disappears?" [7]. Potentially, it can also be chosen not to start or continue an activity that gives rise to the risk, and thereby desist from taking on the risk [1].
When avoiding a known risk, it is important that one is aware of not taking on even greater risks in the process that could result in more severe consequences.
Risk avoidance within opportunities are different, as it most often does not make sense to avoid an opportunity. One would rather seek to meet the risk, and the corresponding action would therefore be Risk Pursuit. Risk pursuit can be done by actively pursuing or continuing the activity that has been assed to cause a positive impact, by manipulating possible positive consequences to maximize estimated gains or by increasing the general likelihood of the risk to elevate positive outcomes [2].
Risk Mitigation
Risk Transfer
Risk transfer is the action where the risk owner transfers the risk (typically a threat) to other parties, by paying the other parti a fee for taking on the risk.[7]. The transfer can be compared to a marketplace, where the risk owner wish to sell some goods (in this case bads as they are threats), but rather than receiving money for the transfer, the risk owner accompanies the transferred risk with money or other considerations that the buyer would then receive[7]. The risk transfer can be done both internally and externally in the project, program or portfolio, but most often it is done through an external transfer to a contractor or similar. The contractor may then seek to transfer the risk on to sub-contractors.
Risk transfer can also be done through insurance. Not all risks can be insured, but choosing insurance as an option spreads out the risk and provides some safety to the risk owner knowing that a worst case scenario can be afforded. Also, from an economical point of view, it can be beneficial to fix a risk cost as it eliminates the economical cost from a potential disruptions the risk could cause, which in the end could blow the budget and thereby be a showstopper for the project, program or portfolio.
Insurance is solely based on statistics, hence it can be difficult to insure new and unknown risks as the insurer will need to have enough data to know that they will statistically profit from the insurance in the long term. Insurance is therefore often seen in construction projects where data is easy available. Like risk transfer to contractors, an insurer can also choose to sell out parts of the insurance to sub-insurers to split out his own risk and carry the risk at a lower premium[7].
No matter what kind of risk transfer is chosen, it is important that all parts of the transfer fully understands the risk and the rewards. If the risk owner transfers a threat to another part and it turns out that the other part is not capable of handling the threat, the owner will be left with the original risk himself, not being able to afford a sufficient treatment. Likewise, if the risk owner transfers a threat that he believes is of great risk, but it turns out that it is not, the owner could have saved a potential high premium by keeping the risk internally[7].
If the risk is an opportunity, it can still be beneficial to transfer or share the risk with other stakeholders if they can either increase the likelihood of the opportunity happening or benefit from the opportunity happening themselves, increasing their motivation to provoke the risk[2].
Selecting treatment options
Application
Provide guidance on how to use the tool, concept or theory and when it is applicable. As mentioned in the Risk Treatment Process, the following steps should be taken before the treatment can occur:
1) Identify the risks 2) Asses the risks) 3) Plan on what you do as treatments on the risks
Insert 4 phases.
- Very useful in programs and portfolios, where risks and treatments can be discovered along the way -
Treatment plans
proposed actions, priorities or time plans, resource requirements, roles and responsibilities of all parties involved in the proposed actions, performance measures, reporting and monitoring requirements.
Development of Treatment plans
Approval of Treatment plans
Implementation of Treatment plans
Limitations
critically reflect on the tool/concept/theory. When possible, substantiate your claims with literature
Limitations to the risk identification and the cost of treatment
Firstly when talking about risks, there will always be the limitation that one is simply not capable of identifying every risk related to a project, program or portfolio as there will be unknowns that we are still not aware of. It could however be argued, that most often risk assessments will identify the most important risks, and thereby be able to mitigate the risks that are a threat to the project, program or portfolio. Also, if one were able to identify all risks, there would still be a limitation to the treatment. Choosing the kind of treatments one wish to implement can be done freely, but there will be a cost related to this treatment. The cost will be a limiting factor, as there will be a budget in where the cost of the treatment will need to stay. Therefore, it is not possible to choose exhausting treatments for all risks which limits one in the possibility of treating the risks.
Secondly, risks that are being identified in a project, program or portfolio are most often based on previous experience or historical data. This works great in larger organizations where the risk exposure stays within the same scope over time. But in especially projects where time and experience on similar projects are a limited factor, this can result in difficulties identifying sufficient risks. There is not much, if any, data to rely on as projects are different from one another. A consequence of this is that the related risks will need to be identified from experience, and this is very much dependent on the people working on the project. If they do not have much experience to rely on, the project will be exposed to an overall greater risk than if people in the project did have a lot of experience.
- Impossible to first of all identify all risks in a project, secondly to create treatments for them
- Risks are often identified through historical data/events. Certain things has happened previously in a project or similar cases, and have therefore been identified and documented as a risk. However, this can be difficult to predict/find data on in a time limited project where a lot of things are new.
- Development of treatment plans can take time and not be useful in shorter projects.
- More ideal for programs and portfolios, where data can be added to already existing data and where the treatment continuously can be developed over time.
- Difficult to quantify the responses and they will therefore often be based on a persons opinion.
Annotated bibliography
Provide key references (3-10), where a reader can find additional information on the subject.
Risk Treatment. (2021, June). ENISA, European Union Agency for Cybersecurity. Retrieved March 19, 2022, from: https://www.enisa.europa.eu/topics/threat-risk-management/risk-management/current-risk/risk-management-inventory/rm-process/risk-treatment
Danish Standards Association, Dansk Standard. (2018, February 19). Risikoledelse - Vejledning, Risk management - Guidelines. DS/ISO 31000:2018. From: https://sd.ds.dk/Viewer?ProjectNr=M296412&Status=60.60&Inline=true&Page=1&VariantID=41
References
- ↑ 1.0 1.1 1.2 International Organization for Standardization (2018), DS/ISO 31000:2018, Risk management - Guidelines, Retrieved from https://sd.ds.dk/Viewer?ProjectNr=M296412&Status=60.60&Inline=true&Page=1&VariantID=41
- ↑ 2.0 2.1 2.2 Risk Treatment. (2021, June). ENISA, European Union Agency for Cybersecurity. Retrieved March 19, 2022, from: https://www.enisa.europa.eu/topics/threat-risk-management/risk-management/current-risk/risk-management-inventory/rm-process/risk-treatment
- ↑ 3.0 3.1 International Organization for Standardization (2009), DS/ISO 31000:2009, Risikoledelse - Principper og vejledning, Risk management - Principles and guidelines, Retrieved from https://sd.ds.dk/Post?ProjectNr=M228821&Status=99.60
- ↑ 4.0 4.1 Refsdal, A., Solhaug, B., & Stølen, K. (2015). Cyber-Risk Management (SpringerBriefs in Computer Science) (1st ed. 2015 ed.). Springer.
- ↑ Watt, A. (2014, August 14). 16. Risk Management Planning – Project Management – 2nd Edition. Pressbooks. Retrieved March 20, 2022, from https://opentextbc.ca/projectmanagement/chapter/chapter-16-risk-management-planning-project-management/
- ↑ International Organization for Standardization (2020), DS/ISO 21502:2020, Project-, programme and portfolio management - Guidance on project management, Retrieved from https://sd.ds.dk/Viewer?ProjectNr=M351700&Status=60.60&Inline=true&Page=1&VariantID=
- ↑ 7.0 7.1 7.2 7.3 7.4 7.5 Damnjanovic, I., & Reinschmidt, K. (2019). Data Analytics for Engineering and Construction Project Risk Management (Risk, Systems and Decisions) (1st ed. 2020 ed.). Springer. https://link.springer.com/chapter/10.1007/978-3-030-14251-3_2#citeas
- ↑ Project Management Institute, Inc. (PMI). (2019). Standard for Risk Management in Portfolios, Programs, and Projects. Project Management Institute, Inc. (PMI). Retrieved from https://app.knovel.com/hotlink/toc/id:kpSRMPPP01/standard-risk-management/standard-risk-management