Risk Register Analysis
Contents |
Introduction
A risk register consists of three main elements. It follows the same basics as the risk management strategy. [2] First and foremost it consists of the risk, secondly, it consists of the cause of the risk, and third it consist of the action of the risk. When building up a risk register these three elements will be covered by the following three steps. The first step is called Identify. Here all possible risk will be identified. The second step is called Assess. The possible risks identified must be evaluated regarding probability and impact on the PPP. The third step is called Plan. The management response is planned to ensure the if a risk materializes, the PPP is not taken by surprise. Creating and populating the risk register tends to be an iterative process since new information can occur in the process and earlier steps need to reevaluated to find the optimal solution. During the lifetime of a PPP, the risk register should be evaluated to ensure the identification of possible new risk or a change in already known risks. The register should as a minimum be evaluated just before the starting of a new phase of the PPP. It is important that threats and opportunities are communicated to stakeholders. This is a continuous process during the lifecycle of the PPP, to ensure that everyone involved knows how to respond if a risk materializes.
Identify
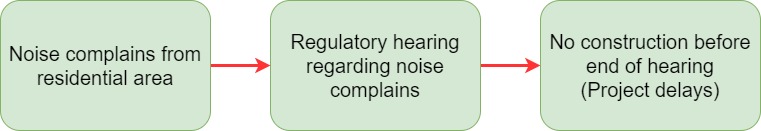
The first step in creating a risk register is the identification of project context. This should be done with respect to the risk management strategy. [2] The context of a PPP is depending on several factors. This includes but is not limited to the organization environment such as legislation and governance requirements, Stakeholders involved in the project and the complexity and scale of the PPP. When the context has been established, the identification of possible risk can begin. When identifying risks, the cause, event, and effect of the risk should be established.
During the identification, it is important to state that risk should not be identified for the sake of creating a large register.
Assess
Plan
Communicate
References
- ↑ Managing Successful Projects with PRINCE2. http://proquestcombo.safaribooksonline.com.proxy.findit.dtu.dk/9780113310593
- ↑ 2.0 2.1 Risk management strategy. http://apppm.man.dtu.dk/index.php/Risk_management_strategy