Portfolio Risk Management Process
Contents |
Abstract
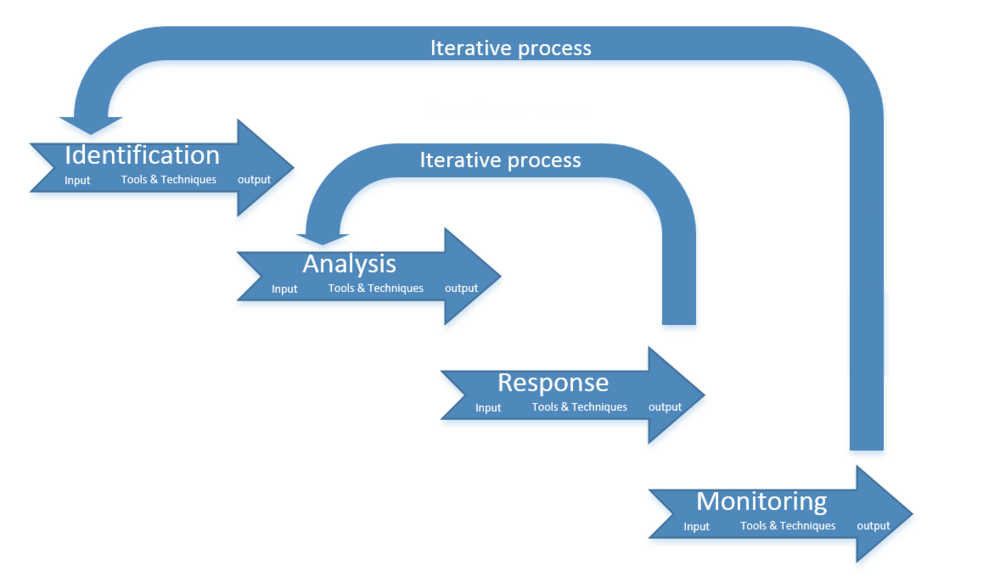
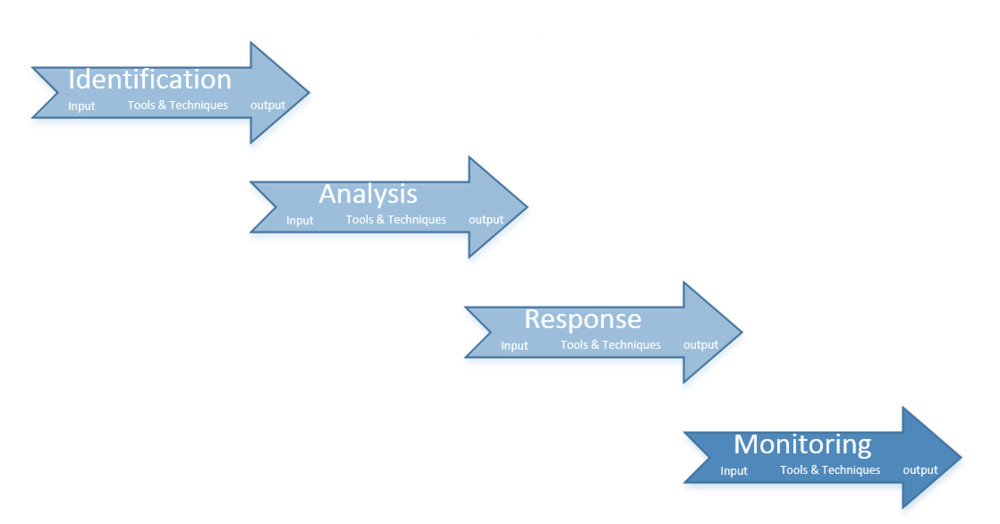
The portfolio manager has to handle several disciplines, where Portfolio Risk Management is one of them[1]. Risks are uncertain. The uncertainties need to be handled to make a solid strategy with as few surprises as possible. This area of portfolio management is critical for success. It is necessary to work through four aspects of Portfolio Risk Management to control the risks a portfolio is affected by. The various aspects are identification, analysis, development responses and monitoring and control. Hence this article will provide a guidance to structure the framework of the processes and the content in the aspects.
The first aspect is identification. In the identification phase all the types of risks regarding portfolio management will be found. When the risks have been found, they will be analyzed. A plan of responses will be developed based on the analysis. The plan consists of concrete actions, when to execute the actions and who that has the responsibility to act, when the situation occurs. When the plan has been set, the assigned manager will monitor the risks and their environment. The portfolio manager will act if needed. The assigned manager keeps a record of new findings and new experiences.
The process of the four aspects should be handled iteratively, so all the aspects are applicable at all times. The first iterative process is from the response phase to the analyze phase. The reason for this is, that the impact of the developed responses have to be analyzed again, to make sure that they work as anticipated in relation to the entire portfolio. Another type of iterative process is occurring, when the conditions of a curtain risk changes and it must go through all the phases again. When new risks occurs all the phases need to be used as described.
Identification of the portfolio risks
It is important to realize, that there are 3 types of risks to identify in portfolio risk management[2]. The types of risks are structural risks, component risks and overall risks. The structural risks are the ones related to the interactions between the components. The components consist of either projects or programs. The structural risks are normally threats in form of resource issues, but can also be opportunities in form of niche qualification in the organization.
Component Risks are normally handled by either the project[3] or program manager, but the component risks get relevant for the portfolio manager, when the risks escalate and expand out of the mandate, that the component manager has. The reason for this is, that the magnitude of these risks might have significant effect on the portfolio or has a strategic aspect or objective. These kinds of risks are normally related to the three parameters of the Iron Triangle, cost, time and scope.
The last type of risks are the overall risks. The overall risks are the risks that emerges, when components interact in the portfolio. The overall risks i.e. all risks that is not defined in the above-mentioned types of risks. The different components can have different objectives, missions or visions, and therefore the components work in different directions. The overall risks can also give the opportunity of distributing "best practice" to other components.

Example: A portfolio has four components, called A, B, C and D. Component B finds best practice in a certain area of expertise, that is applicable in component A and D. This gives the opportunity to optimize A and D based on the development in component B.
Inputs
The identification phase has various kinds of input, that can be used to specify the risks in a portfolio. The main categories[2] are the Enterprise Environmental Factors, Organizational Process Assets, Lists of Selected Portfolio Components, Portfolio Management Plan and Escalated Component Risks. It is important to consider which types of inputs, that is relevant for the specific portfolio[4].
Enterprise Environmental Factors is the public information, that affects the portfolio e.g. academic studies and benchmarking among others. In some experienced company’s internal databases are used by sharing gained knowledge throughout the organization, these historical files are called Organizational Process Assets. A third type of input is the list of selected portfolio components, which commonly acts as the baseline of the estimated risks.
Portfolio management plan provides input from a higher level of management regarding scheduling, risks, cost and quality. The Portfolio management plan shows the known risks in the plan, it allocates the responsibility and budgets, where the risk fee is included. The risks will often be illustrated in a Risk Breakdown Structure.
The last type of input is the Escalated Component Risks. It is heavily related to the type of risks called component risks. It is the ones that has escalated out of the component managers mandate.
Tools and Techniques
In the process of identifying the risks and making a Portfolio risk register some tools and techniques are very useful. The different tools and techniques[2] are called Documentation Reviews, Information Gathering Techniques, Checklist Analysis, Assumptions Analysis and Diagramming Techniques. All the tools have pros and cons. It is important to use the appropriate tools and techniques for the specific situation[4].
The Documentation Reviews is based on big data gained on component management level and matched it with the portfolio management objectives. The Information Gathering Techniques is done by either the Brainstorming technique[5] [3] , Delphi technique [6] [7] (The Delphi Technique in Project Management), Interviewing, root cause identification or SWOT analysis. The brainstorming is an effective way of making the framework of the identification. It can be done by gathering a group of experts, that simply empty their brains in order to get every possible risk on the table. After this exercise the experts organizes the risks in a risk breakdown structure.
When different agendas cloud the objectivity of the process the Delphi technique can be used. The participants of the Delphi technique are a facilitator and a group of experts. They at some point anonymously agree to the facilitators questions regarding the risks.
Interviews can be used to interpret the risks. The participants can be stakeholders [8] [9], component participants experts, sponsors and so forth.
Properly the most effective tool is the Root cause identification. As the name suggests, the tools focus on the root of the risks. The tool can also be used with the risk breakdown structure, where the risks are categorized by the roots of the risks.
To get a broader perspective the risks related to the dimensions of SWOT-analysis can be effective. It gives both the in-house perspective in relation to strength and weakness and the outgoing perspective of opportunities and threats.
The Checklist Analysis is a nice quick way to identify the risks. Keep in mind, that it is based on previous experience and new aspects will often be missed, when using this tool. When used on routine work it is very effective.
The Assumptions Analysis on the other hand, can identify risks, which hasn’t been experienced. Possible assumptions are tested and the outcomes are assessed and validated. The tool is efficient for "thinking out of the box". It has the constraints of the participants imagination. Hence it is important to keep the unknown risks in mind.
The last type of tool is the Diagramming Techniques. It is basically visualizations of causality in relation to possible risks and portfolio objectives e.g. cause-and-effect diagrams, system or process flow charts and influence diagrams. The tools can also help categorize the risks e.g. Risk Component Chart amongst others.
Outputs
The Output of the Identification is the Portfolio Risk Register. It is a supplement to the Portfolio management plan. It consists of a list of identified risks, risk owners, list of potential responses, root causes of risks and updated risk categories. It is basically a summarize of the work above. I.e. The risks are lined up with the immediate dedicated manager and the mandated responses. It might also contain the root of the risks, if it is known. The Portfolio Risk Register should be updated, whenever it is needed[2].
Analyze Portfolio Risks
Input
The input[4] for the Analyze Portfolio Risks phase is the output of the Identification phase. The input of the Analyze Portfolio Risks is as mentioned above the output of the Identify Portfolio Risks. It consists of the Portfolio Risk Register and the Risk Management Plan[2]. The risks found in the identification phase will be analyzed. The risks will be prioritized based on the impact and the probability. The impact can have different parameters e.g. financial, environmental, strategic et cetera. The tolerance of the risks will also be a part of the analysis. The time gives an extra dimension to the analysis in terms of immediate responses to the risks. If the information is subject to bias or in other ways not comprehensive the acting manager should gather the missing information. The analysis must be checked routinely to make sure, that the assumptions hasn’t changed, and if so a new analysis should be made.
Tools and techniques
The tools used for the analysis is normally divided in two categories. The Risk Probability and Impact Assessment and the Risk Combining and Modeling Techniques[2]. Risk Probability and Impact Assessment investigates the probability of a certain risk of happening and the actual impact if it happens. It is very important to keep the quality of the input in mind during this process. The risks should be formulated in measurable variables and parameters in order to calculate the probability as objectively as possible. The bigger the amount of data is the better. The probability is normally visualized in distributions e.g. normal distribution.
The impact and probability is typically investigated by experts in the interviews or Delphi technique. The impact and probability is not worth much without each other. Hence the two are often combined in the analysis with tools like Probability and Impact Matrix [7] (Risk matrix) or financial tools (Best Practices for Project Portfolio Selection), that can be combined with Scenario Analysis.
The Risk Combining and Modelling Techniques analyzes the components both in terms of structure and composition. The analysis reaches beyond the accumulated risks of the components, that escalates in magnitude into the portfolio level. It also investigates the risks that exists because of the interaction of the components. It is typically done by using sensitivity analysis and modelling and simulation.
The Sensitivity Analysis investigates the risks with the biggest impact on the portfolio. It does that when the other parameters are held to the baseline. It shows the sensitivity of on parameter, which is not the worst-case scenario, but a relatively more likely scenario. The visual output of the Sensitivity Analysis could be the tornado diagram. This is a strong tool for prioritizing the risks and where to focus the action and response.
The Modeling and simulation could be a Monte Carlo Technique [10] (Monte Carlo Simulation of Risk). The simulations and Modeling is based on parametric optimization. The parameters can be several portfolio objectives, that is iteratively randomly simulated. The parameters can have financial, time, quality aspects and basically every important measurable variable can be a parameter. The iteration is typically computer generated. The output can be the most likely scenario or the worst-case scenario.
Output
The output of the Analyze Portfolio Risks is an update of the Portfolio Risk Register and a Portfolio Risk Exposure charts. The update consists of a ranking of the list of portfolio risks. The priority can be divided into different objectives and give the portfolio manager a better overview on the objectives. The risk breakdown structure should be categorized into either root causes or portfolio objectives by now. Some immediate responses can be a part of the output, but focus should but on the risks impacting in the near future. The risks that is not prioritized should be formulated on a watch-list for monitoring. Since the processes is iterative, some of the risks will occur in the analysis more than once. Therefor information about overall trends should be gathered to control if the anticipated affect is accordingly.
Portfolio Risk Exposure Charts illustrates the probability of the portfolio reaching either tangible or nontangible objectives, even though risks mainly are formulated measurably. The cumulative distribution can for instants show the probability of a certain magnitude.
Developed responses based on the analyzed risks
In this phase the portfolio manager must develop responses on the prioritized risks from the analysis. The manager should implement the risk responses into the budget, schedule and portfolio management plan. The responsibility should be clearly defined, which means that risk owners are dedicated to the specific risk and knows how to respond on specified developments regarding the risk and when to contact the superior, if the risk expands out of mandate.
Input
The input of the response development phase is updated Portfolio Management Plan and Portfolio Risk Register (Risk register ). A List of Prioritized components within Each strategic category is needed for this phase also[2].
Tools and techniques
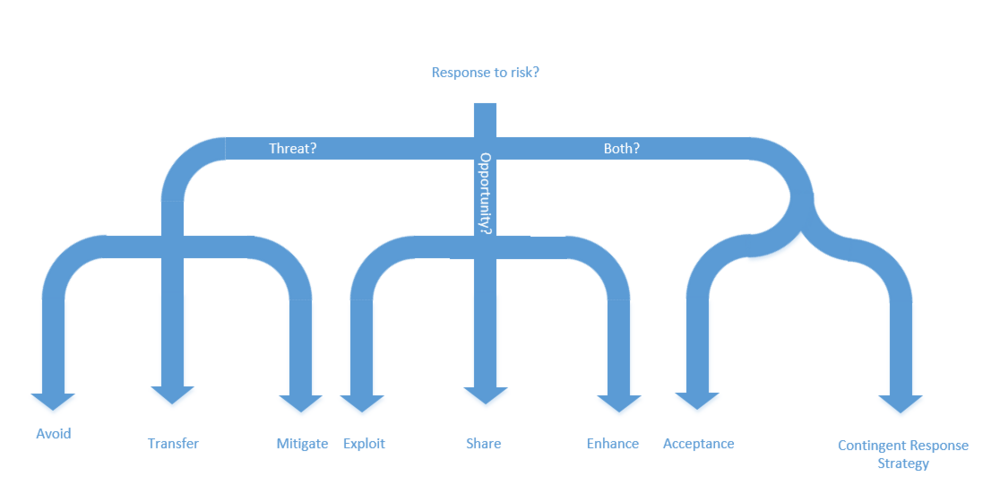
The risks can be handled in several ways. Responses doesn’t have to be one solution. It can easily be a combination of responses. It is also recommended to have a fallback plan or maybe two. The risk is often met by a curtain budget and timeframe. The Response Strategy Selection is a variety of responses, that mainly focus on the type of risk and the wanted exposure towards the risk. The responses combined with scenario analysis[11] [12] might help to predict future situations[2].
The response strategy can be handled in a lot of ways. In order to structure the approach, the responses can be divided into risks in form of threats, opportunities or both. The threats can be handled in three ways. The manager can either try to avoid, transfer or mitigate the threat. In order to avoid the threats, the portfolio management has to be changed. It can be done by choosing another approach for the same objectives, so the portfolio avoids the threat or completely change the objectives of the portfolio, because the objective is not worth the threat.
Another strategy is transferring the potential threat. It can be done by transferring responsibility of the threatening part of the portfolio. It is mainly used transferring the financial exposure e.g. insurance, guaranties, performance bonds etc. The transfer is normally dictated by law or contracts.
The third way of dealing with risks is to mitigate. When mitigating the threat reduces in probability, impact or both to the acceptable level. It can be done by splitting the risk or taking early action.
Risks are as earlier mentioned also opportunities. They also need to be handled in order to optimize the opportunity exposure in the portfolio. The three opportunity strategies are exploit, share and enhance.
When exploiting the opportunity, the manager tries to make sure gaining from the opportunity. This can be done by e.g. allocating more resources in terms of working hours or material. It can also be done by hiring new employees with new or better competences.
If it’s not possible to exploit the opportunity, sharing can be the way to go. When sharing the opportunity another party is broad in. The other party gets a part of the gain in return of raising the magnitude or chances of realizing the opportunity. This can be done by establishing partnerships e.g. joint venture, special-purpose companies etc.
The last recommended technique for handling opportunities is enhancing. This means that the value of the opportunity is increased in terms of impact and probability. This can either be done by raising the chances of the trigger conditions or by targeting the impact drivers in order to make the project or programs effect on the portfolio greater.
Other responses can be used for both opportunities and threats. The strategy, Acceptance, can either be passive or active. In the passive acceptance the Portfolio manager acts when the risk occurs without planned responses. When using the active acceptance, the responses can be planned and time and resources is allocated to handle the risks, that is expected. Beside this the active approach might include allocations for unknown risks.
Contingent Response Strategy is another type of strategy to handle both threats and opportunities. The predefined response is used if certain trigger conditions occurs. This strategy can be used if the trigger conditions has clear warnings in time to incorporate the planned response.
The scenario analysis can also be used, as earlier mentioned. It is basically several responses based on different outcomes. In order to find appropriate causality of responses and risks the previous steps, identification and analysis might be necessary.
Output
The output of the developed responses is the updated versions of previously mentioned Portfolio Risk Register, Portfolio Management plan and Portfolio components. The Portfolio risk register has new elements, which is:
- Response strategies and actions related to the strategy.
- Trigger plans and related conditions and warning.
- Allocated budget and time for risks in project[3], program and portfolio level.
- Fallback plan if the planned responses doesn’t have the estimated and wanted effect.
- Risks, which is created by responses and related strategies.
- Expected risks after responses has been executed, consisting of primordial accepted risks and new accepted risks.
The updated the Portfolio Components includes reevaluated and rearranged components in the categories. The portfolio component might also need to be re-balanced in order to keep the susceptibility of the portfolio. The Portfolio Management Plan is also updated in terms of contingency reserves, schedule and resources to an extent, so the portfolio manager can monitor the risks and its environment and know how to respond when trigger conditions happen[2].
Monitoring and controlling Portfolio risks
In this phase the portfolio manager controls the risks by using the previous defined responses. The risk owner has also been defined in this phase. This is done by the following actions, that is defined in “The Standard for Portfolio Management”. The following elements should be monitored[2]:
- Risks
- Trigger conditions
- Contingency plans
- Residual risks
- Stakeholders[8] [9] (Stakeholder Management )
- Risk responses
- Efficiency of the risk responses
The monitoring phase contains also the identification of emerging risks. The portfolio manager should also analyze and develop responses to both emerging and existing risks. The existing risks are included because the environment of the risks changes during time. The portfolios attitude towards susceptibility or strategy might change as well.
Input
The input consists of Updated Portfolio management plan, Portfolio Risk Register, Component Progress Report and additional Component Data.
Tools and techniques
When the Portfolio risks must be monitored a handful of tools and techniques are useful. Portfolio Risk Audits focuses on the documentation of the effectiveness of the risk responses. Based on the performance data the portfolio manager finds trends in order to ensure the forecasts still points in the direction of the portfolio strategy. This type of tool is called Variance and Trend Analysis[2].
Status Meetings[3] (Meeting strategies ) should be incorporated as a periodic event, where the discussion focuses on newly identified risks and walk them through the phases of Portfolio Risk Management.
The last tool for monitoring is the Portfolio Risk Reassessment. This tool is used to identify, analyze and develop responses to new risks. This technique is also used if the risks escalate into unanticipated areas for instants if risks emerges from the watch-list into a priority-list. The risk environment can change in impact or probability; thus, a reassessment must be done. The Reassessment must be done in the entire lifecycle of the portfolio.
Output
The output consists of the Portfolio Change Requests, Portfolio Risk Register and Organizational Process Assets. An integration of responses in the Portfolio Management Plan is done in the Portfolio Change Requests together with the chosen way of monitoring.
The new elements in the Portfolio Risk Register is the outcomes from the Portfolio Risk Reassessment, including an update of the described elements. The Risk Register also contains documentation of the actual risk evolvement and the efficiency of the responses for future use.
The last element of the output is the Organizational Assets. The four phases should contribute with some organizational changes in the processes, if it is needed[2].
Conclusion
The four phases that is described above shows an overview of the phases and their content. This Guide should provide the framework for Portfolio Risk Management. When the guide has been followed and reflections has been made regarding appropriate tools and techniques, the Portfolio Risk Management Processes should provide good management guidance in relation to risk susceptibility by using structured and effective responses. The organization is also provided with the opportunity to optimize the processes in the organization in terms of risk control.
Limitations
Portfolio Risk Management is obviously not the whole truth. It tries to predict how the risks evolve. The methods in the described process and the process itself has some limitations. Some of the is stated below:
- The entire investigation assumes, that the world will act in the way we have seen before.
- Unforeseen events will happen randomly.
- The investigation should be support to the decisions, but the manager shouldn’t make decision entirely based on the results of the investigation.
- It is not always worth using time and money on the risk manager, if the risks are to insignificant or simply cannot be implemented.
- The assumption that human behavior can be predicted can also be challenged. Humans has always evolved and their behavior is to some extent unique.
- Mega-trends can be extremely difficult to forecast and the investigation is to some extent depended on the mega-trend assumptions.
- In a rapidly changing world where the risk environment changes all the time, the risk manager should ask himself, if he can make his forecasts before the environment changes again.
Annotated bibliography
The Standard for Portfolio Management, Second Edition, Project Management Institute, 2008 is one of the standards in the field of Portfolio management, hence he credibility is very high. It focuses more on the Risk Management than other standards, but has the same framework regarding the processes as most standard, just more detailed. It gives a good overview of all the portfolio management aspects.
A Guide to the Project Management Body of Knowledge (PMBOK® Guide), Fifth Edition, Project Management Institute, 2013 is one of the most well-known standards in the field of project management, hence it also has great credibility. It is great for getting to know, what the components in the portfolio consists of.
Management of Portfolios, Office Of Government Commerce, TSO, 2011 Gives a broader perspective to the duties of the portfolio manager. It is also a very well-known and the credibility is high as well. It is on the other hand not very good for Portfolio Risk Management.
References
- ↑ Management of Portfolios, Office Of Government Commerce, TSO, 2011
- ↑ 2.00 2.01 2.02 2.03 2.04 2.05 2.06 2.07 2.08 2.09 2.10 2.11 2.12 2.13 2.14 2.15 The Standard for Portfolio Management, Second Edition, Project Management Institute, 2008
- ↑ 3.0 3.1 3.2 3.3 A Guide to the Project Management Body of Knowledge (PMBOK® Guide), Fifth Edition, Project Management Institute, 2013
- ↑ 4.0 4.1 4.2 Risk management in a multi-project environment An approach to manage portfolio risks Rolf Olsson, Bombardier Transportation, Vasteras, Sweden, 2007
- ↑ Wilson, C. (2013) Brainstorming and beyond: A User-Centered Design Method. Morgan Kaufmann.
- ↑ Linstone, H.A. and Turoff, M. (eds.) (1975 and 2002 reviewed version) The Delphi Method Techniques and Applications.
- ↑ 7.0 7.1 Geraldi J., Thuesen C., Oehmen J., How to do Projects, Version 0.5
- ↑ 8.0 8.1 Developing Stakeholder Theory, Andrew L. Friedman and Samantha Miles, Journal of Management Studies 39, January 2002
- ↑ 9.0 9.1 Managing successful projects with PRINCE2, TSO, 2009
- ↑ Danish Standards,ISO 31000 Risk management - Principles and guidelines 2009
- ↑ Hindle, T., (2008), “Scenario Planning”, The Economist, online article: http://www.economist.com/node/12000755
- ↑ Roxburgh, C., (2009), “The use and abuse of scenarios” online article: http://www.mckinsey.com/business-functions/strategy-and-corporate-finance/our-insights/the-use-and-abuse-of-scenarios